Set up an Airwall Relay to Route Encrypted Connections
An Airwall Relay routes encrypted Airwall Edge Service connections across all networks and transport options, without modifying the underlying network, for secure end-to-end connectivity.
- Supported on these Airwall Gateways:
-
- Physical – 300 Series, 400 Series, and 500 Series
- Virtual – 300v on VMware ESXi, Hyper-V, RackSpace, Xen, and XenServer
- Cloud – 300v on Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP), and Alibaba Cloud.
With an Airwall Relay in place, you can dynamically and easily network any device or group of devices across any public, private or hybrid network, including subnets that are located on separate underlays. The Airwall Relay brokers connections between Airwall Edge Services, based on policies set by the Conductor.
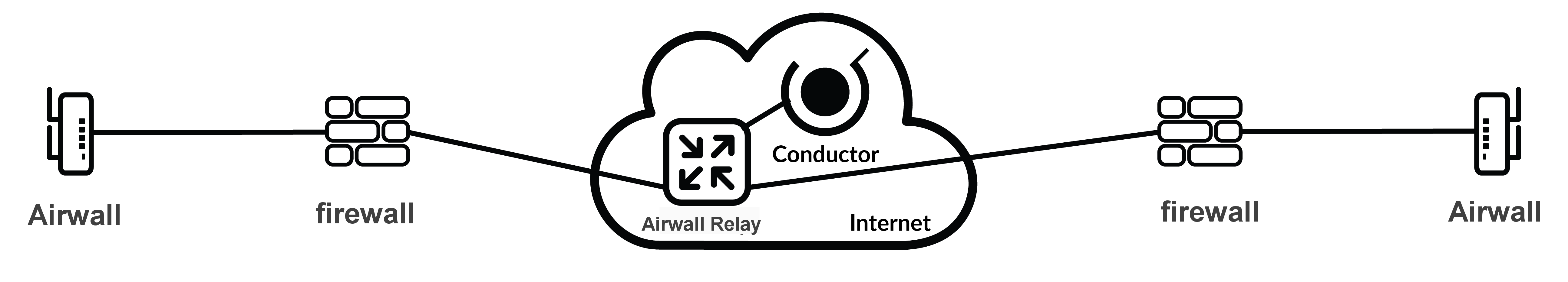
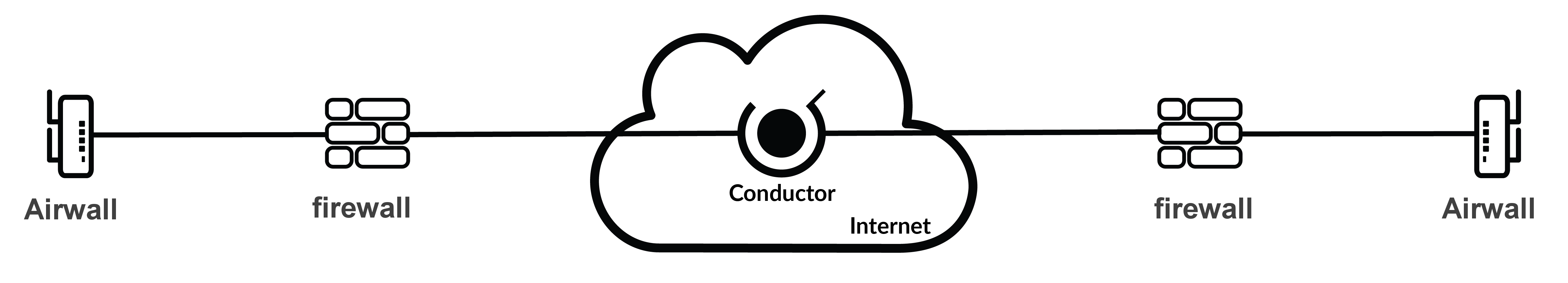
In the illustration below, two Airwall Gateways exist in different underlays. Each Airwall Gateway can connect to the Conductor, publish their IP addresses, and come online. However, communication between the two cannot occur as both Airwall Gateways do not have publicly available IP addresses.
To solve this limitation, add an Airwall Gateway acting as an Airwall Relay. In the Conductor, the Airwall Relay acts as a broker between the two Airwall Gateways.